Have you assessed the business impact of a one-hour cross-site VPN outage?
For organizations with multinational or remote operations, VPN(note1) stability is critical to supporting both production activities and business operations. As enterprises evaluate disaster risks and recovery plans, ensuring reliable VPN connectivity remains a key focus.
However, as telecommunications infrastructure has continued to mature, VPN disruptions are now rarely caused by carrier networks or telecom facilities. Post-incident analysis shows that the majority of VPN failures originate within the enterprise environment itself. A key driver is the growing prevalence of compromised systems, as internally managed endpoints can flood VPN infrastructure with excessive traffic, overwhelming capacity and causing service outages that directly impact productivity and business operations.
To effectively prevent such incidents, IT teams must move beyond traditional reactive troubleshooting that begins only after failures occur, and instead establish a network operations model with built-in intelligent self-analysis capabilities.
Note 1
the term “VPN” broadly refers to all cross-regional networking technologies, which typically fall into two categories: self-managed deployments and carrier-provisioned services. VPN tunnels built over the public internet using self-owned equipment offer lower costs but often suffer from limited stability. By contrast, carrier-provided VPN services or dedicated lines deliver higher reliability, though cross-border deployments can be prohibitively expensive. As a result, preventing the overuse of these high-cost VPN links is a critical responsibility for IT operations teams.
N-Partner applies automated flow learning and analytics to enable intelligent network operations
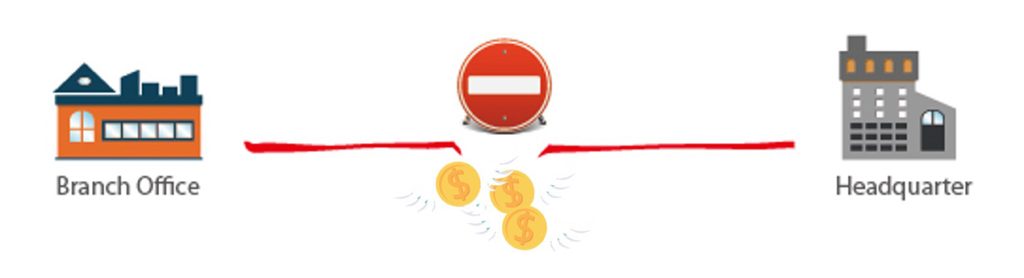
N-Partner applies big data analytics to continuously learn from network traffic data and build dynamic, data-driven baselines for individual IPs, departments, and servers.
By comparing traffic consumption every minute, the platform detects abnormal surges in bytes, packets, or session and accurately identifies both the originating source IP (usually the attacker), and the destination IP(usually the victim). Also, real-time alerts allow operations teams to respond quickly, eliminate disruptions, and make daily operations easier.
What sets this big-data-driven learning capability apart is its ability to operate without manually defined thresholds. Rather than requiring IT teams to set threshold for every IP, the system continuously learns what “normal” looks like, sends alerts in real-time, and accelerates recover before issues escalate. This approach scales effectively across complex networks and large user populations, delivering precise root-cause identification without the delays inherent in legacy, ticket-driven troubleshooting models that depend on post-outage data collection and manual analysis.
In addition to automated intelligence, breaking the network into logical domains for behavioral monitoring provides a scalable approach to operational governance. Whether defined by location, department, access layer, or service role, this segmentation allows traffic to be analyzed in context and summarized through clear, structured reports. As a result, IT leaders gain an at-a-glance understanding of how network resources are being consumed across all business units and environments under their responsibility.
Using the same analytics approach, the solution builds dynamic baselines for each business unit and automatically detects abnormal traffic spikes. With built-in drill-down analysis, IT teams can quickly identify which IP addresses or user activities are causing network disruptions. Once the root cause is addressed, normal network operations can be restored quickly, reducing downtime and preventing repeat incidents.
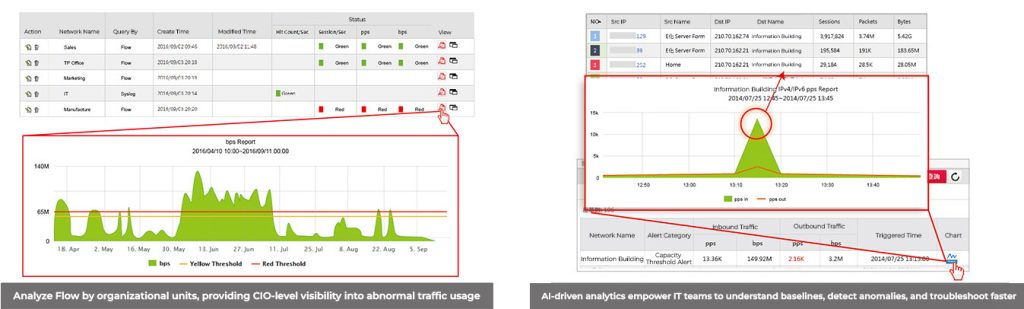
Correlating flow analysis with AD and SNMP to identify users and switch locations
Beyond big-data learning and real-time anomaly detection, N-Partner delivers another core capability by correlating three foundational network management technologies: SNMP for health and status monitoring, flow for traffic analysis, and syslog for behavioer nsight. By bringing these data sources together, the solution gives IT operations teams a clearer, more complete view of how users actually interact with the network.
When abnormal traffic is detected, Active Directory login data identifies the associated user, while SNMP information reveals the exact switch and interface involved. This level of visibility enables IT teams to move quickly from detection to resolution without relying on guesswork or manual cross-checking.
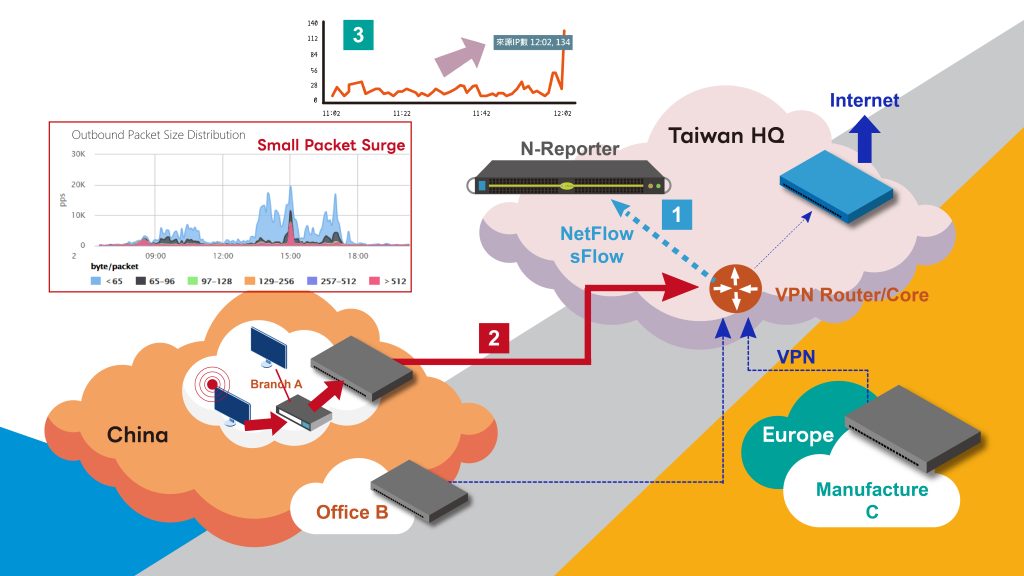
Solution workflow for rapid VPN anomaly resolution
Step 1
To ensure maximum visibility, comprehensive flow data is collected across the entire network. NetFlow and sFlow records are exported from key network nodes, including core switches, VPN gateway routers, and internal core devices at remote sites, and sent to the N Reporter and N Cloud for behavioral learning and anomaly analysis.
Step 2
When any department or IP address begins generating traffic or packets that deviate from its normal behavior, the N Reporter and N Cloud platform detects the anomaly immediately. Monitoring is not limited by the number of IP addresses and covers both internal networks and external sources that generate unusually large volumes of traffic.
Step 3
Once abnormal traffic is identified, the platform proactively triggers alerts and visualizes key indicators such as total traffic volume and packet size distribution. Through interactive charts and drill down analysis, IT administrators can clearly identify the source IP, username, traffic volume, associated department, and the physical location including the connected switch and interface.
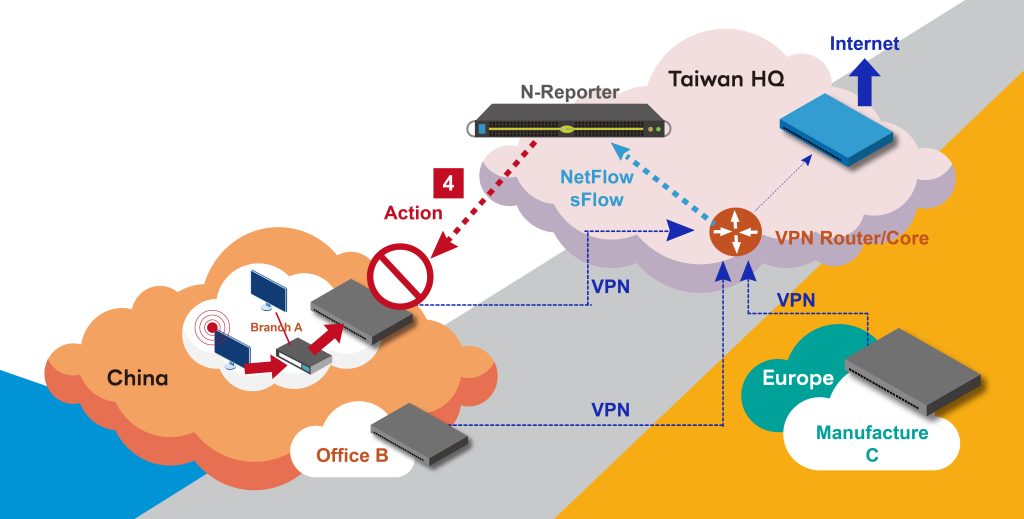
Step 4
Based on the identified source IP and its physical connection point, N-Reporter/N-Cloud pupports coordinated response actions. Blocking commands can be issued automatically or manually to security controls deployed at the VPN gateway, stopping abnormal traffic before it continues to flood the VPN network. This protects critical VPN resources from misuse and prevents further escalation of operational impact.
In addition, by correlating SNMP, flow and syslog, N Reporter and N Cloud can determine the physical switch location to which a malicious IP is connected. This enables an alternative response option that operates closer to the source of the attack, allowing blocking actions to be applied directly at internal network switches. IT administrators can also define automatic unblock rules based on operational needs, while all IP addresses blocked through collaborative defense are recorded for future review and auditing.
Note 2
The set of security devices that currently support coordinated blocking commands from N-Reporter and N-Cloud may change over time. For the latest list of supported devices, please contact N-Partner or an authorized channel partner