Have you assessed the potential business impact if users are unable to log in to the domain or if their credentials are compromised?
As enterprises continue to deepen their reliance on IT systems, the use of Windows domain authentication for user access control and authorization management has become widely adopted. From a defensive security perspective, however, this model also presents a critical weakness: once attackers obtain valid domain account credentials, they effectively gain access to enterprise IT resources. As a result, password brute force attacks remain one of the most common threat vectors.
In many cases, attackers compromise internal endpoints and deploy brute force tools within the corporate network, repeatedly attempting Windows account logins at scale. To mitigate this risk, IT teams typically enforce account lockout policies that restrict the number of failed login attempts and temporarily disable accounts that exceed defined thresholds. While this approach is often unavoidable, it can introduce significant operational side effects. Large scale brute force campaigns frequently result in widespread account lockouts, preventing legitimate users from accessing domain services and IT resources, and ultimately disrupting normal business operations.
To effectively prevent these incidents, IT teams must move beyond reactive, ticket-driven troubleshooting and redesign network operations around intelligent, self-analytical capabilities. When a brute force attack begins, the system can immediately pinpoint the source IP and its physical location, trigger alerts, and enable rapid isolation of the attack source before broader disruption occurs.
Building intelligent network operations through automated event learning and analysis
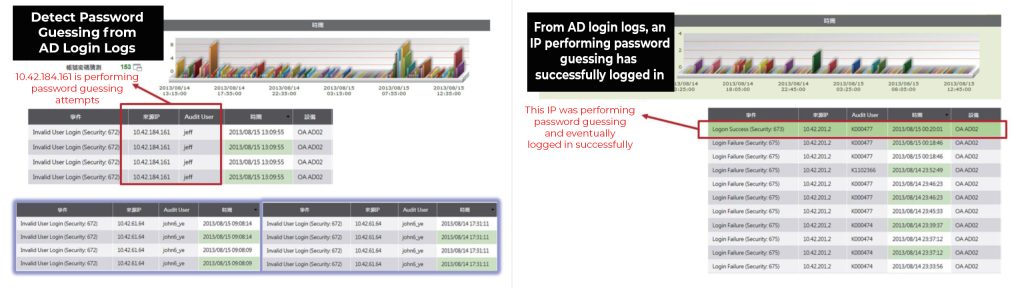
N-Partner uses data-driven analytics to continuously learn from Windows Active Directory authentication logs and establish a baseline of normal login behavior. When login failures suddenly spike beyond expected patterns, the system immediately alerts IT operations teams, clearly identifying the source IP and the accounts being targeted.
In addition to detecting brute force login attempts, the solution also monitors what happens next. If a large number of failed logins is followed by a successful authentication, the event is flagged as a potential credential compromise. This is especially critical when the affected account holds elevated privileges. Early warning allows IT teams to respond quickly by resetting credentials and containing the risk before compromised access leads to broader system misuse or significant business loss.
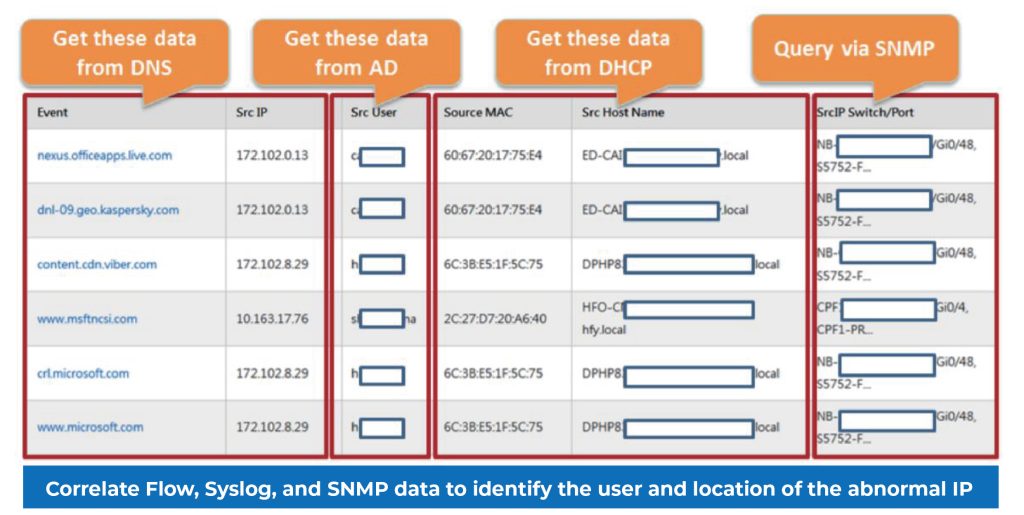
Correlating flow analysis with AD and SNMP to identify users and switch locations
N-Partner delivers a core techonology by correlating 3 network management approaches: SNMP for health and status monitoring, flow for traffic analysis, and syslog fo user behavior. By integrating these data sources, IT operations teams gain a clearer and more detailed understanding of how users interact with the network.
Beyond analyzing and alerting on abnormal Active Directory authentication activity, user identity information derived from Windows AD login logs also serves as a critical link for correlating additional logs and traffic analysis results. This allows IT teams to quickly determine which user was associated with an IP address generating abnormal traffic or attack behavior. When combined with SNMP data, the solution further identifies the physical location of that IP within the network, including the specific switch and interface involved.